Fluency Introduction
Fluency Introduction
A short view of the platform and the operating model behind Fluency security workflows.
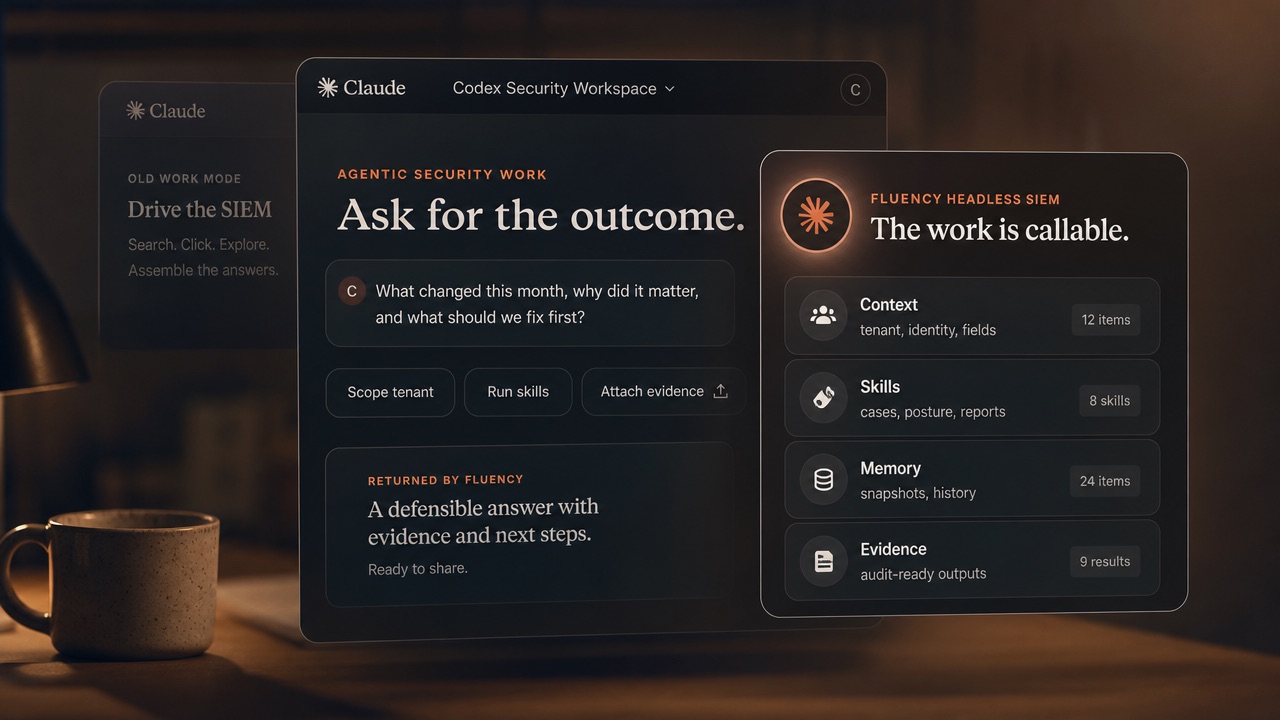
AI agents like Claude Co-Work and Codex are only as capable as the tools underneath them. If your SIEM only exposes screens, searches, and narrow API calls, the agent is boxed in too.
Fluency exposes security work itself: governed skills, functions, context, evidence, and outcomes that people, APIs, automations, dashboards, and AI co-workers can safely call.
On-the-fly answers
Ask the question you need answered. Fluency turns governed data, workflow context, and security logic into customer-ready reporting on the fly.
Ask Fluency
Coverage, health, posture, billing, and service-review reporting become answers you can request, refine, and share.
Which tenants are unhealthy right now? Where did ATT&CK coverage improve this month? Which data sources are silently degrading? What detection gaps should we fix first? Which customer needs a service review this week?
Report examples
Auto-rotating through reports
One deterministic foundation
Headless SIEM does not mean handing security work to a black box. Fluency keeps the logic, data access, policy guardrails, and infrastructure consistent while letting each team choose the interface that fits the work.
Traditional
Dashboards, reports, search, alerts, and analyst workflows for teams that want direct control.
AI-native
Questions, requests, workflows, and analysis through assistants without bypassing security policy.
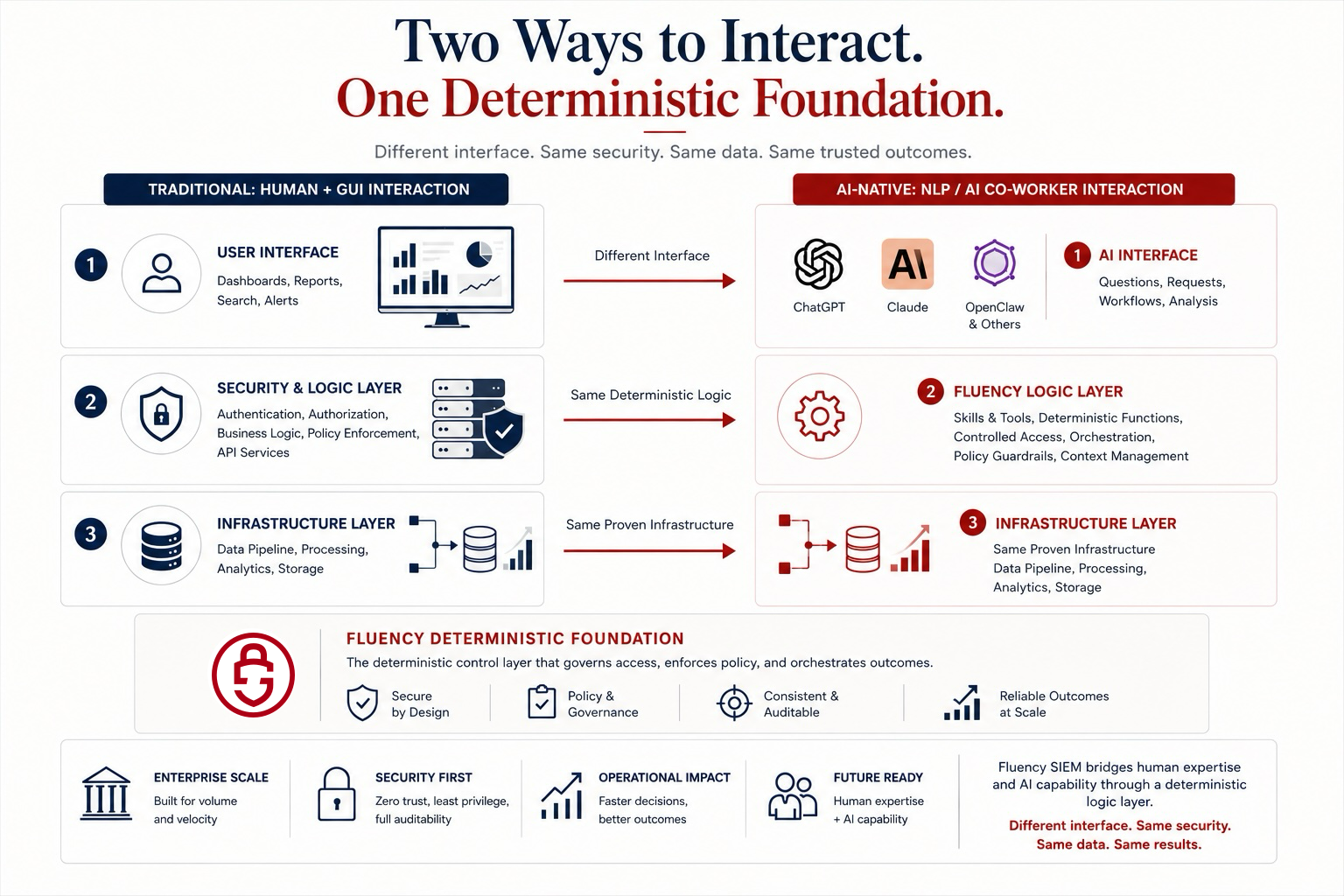
Authentication, authorization, governance, and policy enforcement stay in one layer.
People and AI draw from the same pipelines, analytics, storage, and evidence.
Workflows stay deterministic, auditable, and consistent across interfaces.
Add AI co-workers and MCP-enabled tools without rebuilding the SOC underneath.
See the platform
Fluency is the deterministic layer underneath the interface. Connect the NLI of your choice, including Claude Co-Work, then start with governed skills and functions your team can extend into real operating workflows.
Fluency Introduction
A short view of the platform and the operating model behind Fluency security workflows.
AI SIEM
See how AI-assisted security work can run through governed workflows instead of another disconnected prompt box.
Operational modes
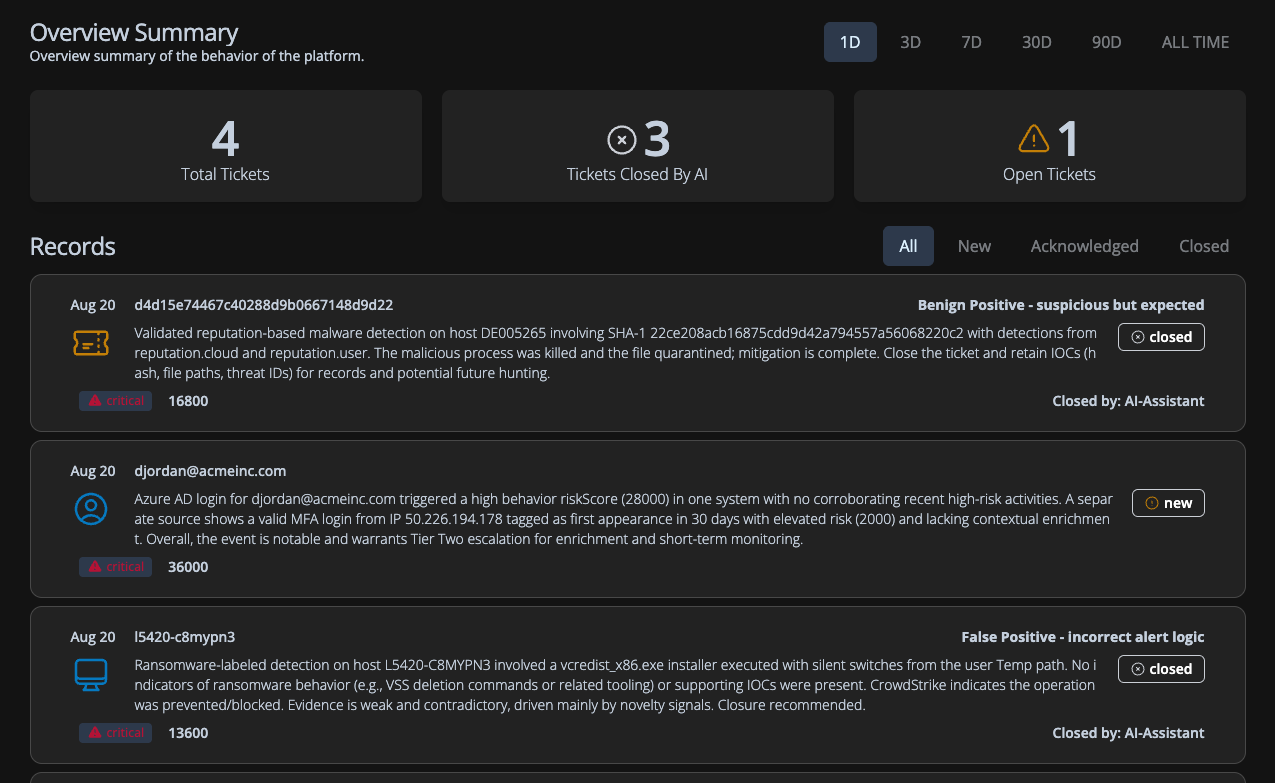
Fluency gives analysts, MSSP teams, automations, and AI co-workers a bounded catalog of security work they can run. Every mode resolves scope, checks permissions, uses known fields, and returns evidence your team can audit.
Ask questions no one dared to ask before, never mind dared to answer. Which tenants are unhealthy? Which signatures need ATT&CK mapping? Which customer has hidden operational risk? Which replay scenario should train the next analyst?
Scope
Resolve customer, grid, account, and resources before work runs.
Status
Check data flow, integrations, degradation, and inactive sources.
Commercial
Summarize periods, licensed users, grid rollups, and snapshots.
Posture
Audit users, endpoint posture, AD hygiene, findings, and reports.
Cases
Triage timelines, repeat actors, fingerprints, and ATT&CK context.
Rules
Draft, validate, compare, map, release, and improve detections.
Training
Turn cases and searches into sanitized scenarios and replay prep.
Safety
Discover fields and facets before workflows query customer data.
Investigation outputs
Fluency turns case data, behavior summaries, MITRE context, fired detections, analyst judgment, and gaps into investigation briefs that can be shared with analysts, customers, and leadership.
Case examples
Auto-rotating through investigations
Built for the AI era
Fluency combines deterministic workflows, behavioral intelligence, risk evaluation, reporting methods, detection engineering, and AI-assisted analysis into work your team can reuse.
AI can help choose what to run while Fluency controls data access, workflow logic, evidence, and output.
Turn investigation procedures, reporting methods, and customer practices into work your whole team can run consistently.
Track what changed across users, systems, timing, access, cloud activity, and risk scores.
Use operational data to spot gaps, prioritize new detections, and map coverage to ATT&CK.
Use Fluency through analyst workflows, natural language, APIs, automation, MCP-enabled tools, and enterprise copilots.
Fluency supports more than 600 organizations across MSSP, enterprise, and government security environments.
Insights & Research
Stay up-to-date with the latest insights on AI-driven security, SIEM technology, and cybersecurity operations from our security experts.
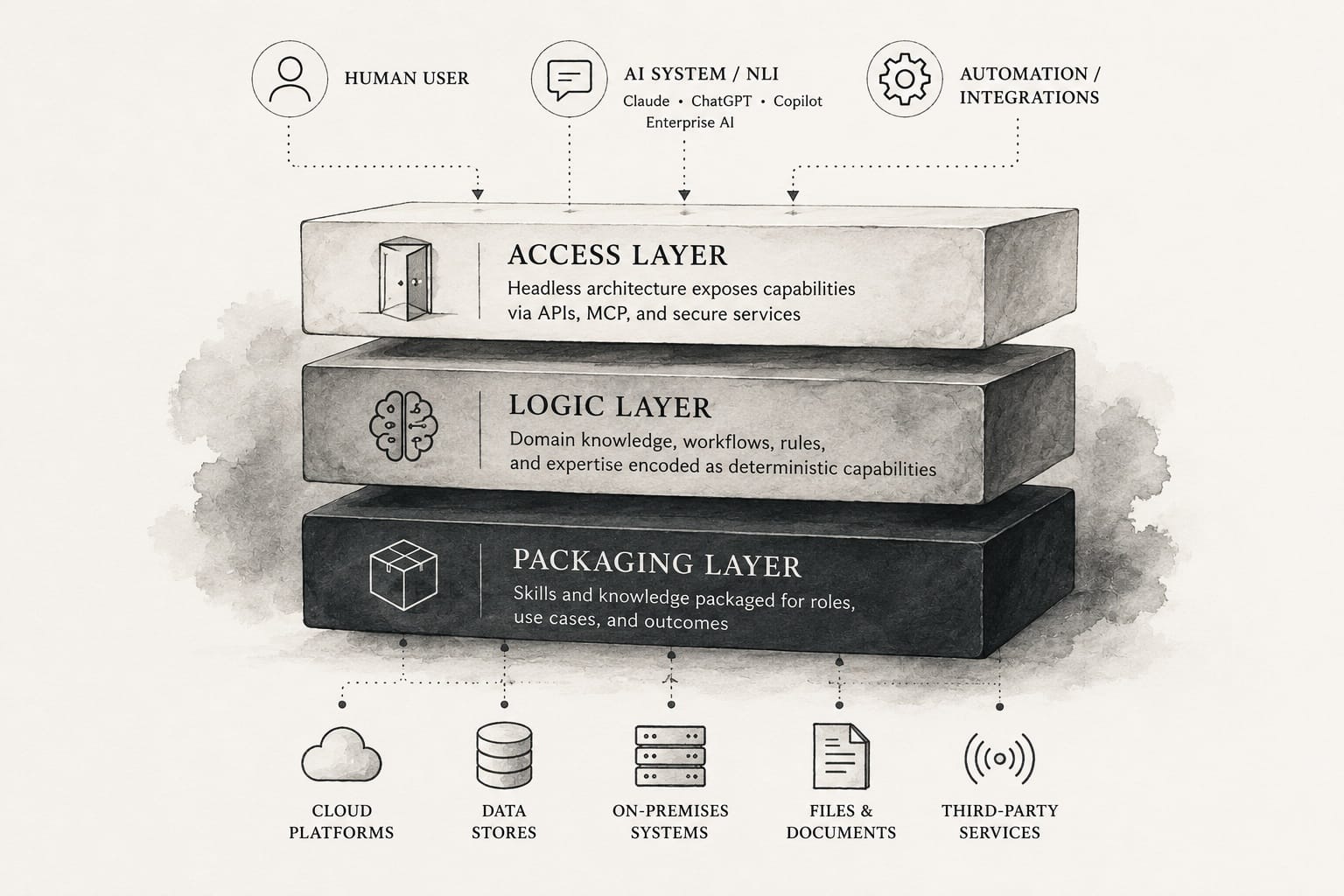
Fluency is releasing a major architectural change designed specifically for AI-assisted operations. The architecture is intended to work with emerging systems such as Claude Co-Work, ChatGPT, Codex, a...
Fluency Security
Security Research

I just got back from two weeks in South Africa. It was one of the more intense business trips I’ve had in a long time. ... But by the end of the trip, it became clear that the real issue underneath al...
Fluency Security
Security Research
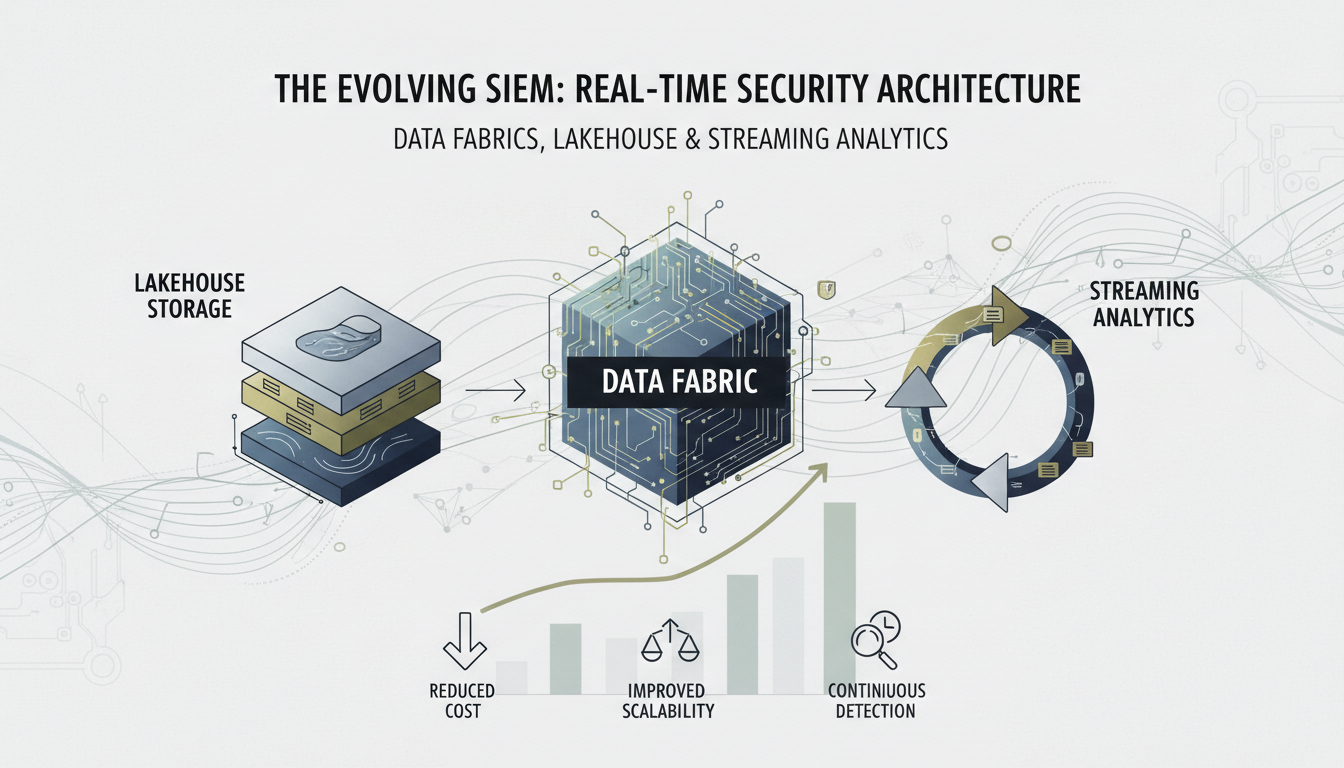
Most people still think of a SIEM as a giant database. You see it in how they talk about platforms like Splunk, Sumo Logic, or Elastic. The conversation is always about storage, search speed, dashboar...
Fluency Security
Security Research
Bring us one investigation, report, detection gap, or customer review your team repeats. We will show how Fluency can turn it into work analysts and AI can run.
"Fluency has consistently met our company's IT needs and has provided extensive support in handling cybersecurity attacks. This is why we choose to renew our contract with them. It has proven to be a valuable investment."